Building agent-first governance and security
Quick Insights
The Bottom Line
Insecure AI agents could create new attack surfaces, increasing enterprise risk by accessing sensitive data.
How This Affects You
The rise of insecure AI agents could compromise personal data held by companies, increasing the risk of privacy breaches and identity theft for consumers.
AI Summary
Companies face new security risks as AI agents increasingly work alongside humans, potentially opening attack surfaces if not properly governed. The Deloitte AI Institute 2026 State of AI report indicates that nearly 74% of companies plan to deploy agentic AI within two years, but only 21% have a mature governance model for autonomous agents. This lack of governance means enterprises may inadvertently treat agents as "first-class citizens" with access to sensitive systems and data, creating blind spots. Andrew Rafla, principal at Deloitte Cyber Practice, states that a robust control plane is essential to govern, observe, and secure how AI agents operate. Without such a control plane, companies risk unmanaged execution and unpredictable, large-scale failures of agent deployments.
Following this story?
Get notified when new coverage appears
This article is part of a story we're tracking:
Should this be getting more attention?
You Might Have Missed
Related stories from different sources and perspectives
 National Security
National SecurityArmy leans on counter-drone marketplace to help address ‘high security concerns’ for upcoming stateside events
“State and local and federal law enforcement officers across the country can purchase from this site. We’ve already had purchases,” Army Secretary Dan Driscoll said. The post Army leans on counter-drone marketplace to help address ‘high security concerns’ for upcoming stateside events appeared first on DefenseScoop .
 Technology
TechnologyNow you can break up with big tech at a bar: ‘cybersecurity disguised as a party’
<p>These digital security organizers bring the fight for online privacy to dance parties, wine meetups and reading groups</p><p>Imani Thompson shows up at Wonderville Bar in Brooklyn looking ready for a DJ set, or to drink, or to dance the night away with friends. While she’ll probably do the latter, she’s also a cybersecurity organizer leading the evening’s event.</p><p>Thompson is the host, along with the New York City-based tech organizing coalition Cypurr Collective, of <a href="https://shaded-tune-076.notion.site/Break-Up-With-Google-2fa921651f1980b7a922d5f07ad89eaf">Break Up With Google</a>. Its purpose isn’t a mystery; the main goal is to help attenders understand how to mitigate their vulnerability to <a href="https://ssd.eff.org/#index">surveillance</a> through major tech services. But it’s also important for people to have fun while they do it, Thompson said – hence the DJs playing until the wee hours of the morning.</p> <a href="https://www.theguardian.com/us-news/2026/ap...
 Technology
TechnologyMaking AI operational in constrained public sector environments
The AI boom has hit across industries, and public sector organizations are facing pressure to accelerate adoption. At the same time, government institutions face distinct constraints around security, governance, and operations that set them apart from their business counterparts. For this reason, purpose-built small language models (SLMs) offer a promising path to operationalize AI in…
 AI & Warfare
AI & WarfareUS security agency is using Anthropic's Mythos despite blacklist, Axios reports - Reuters
<a href="https://news.google.com/rss/articles/CBMivwFBVV95cUxPZVQxQUdjUjgtWnUzUnNfXzI5WFdiMXNkOC1qakZhZ0hfMEZvUVBpckJXQWlFTkdKTzljaU1vQm5hSDFOY3ZHc2p3M1pSSVp5enZuS0VfS3RiT3o4MWx4MnE2dkNHaWNDNVZlR0xUZDRpbEc5eW83V3BmQm9CX1JTeWxvdXJubnJwT19lTXJaLUotTzJ6X1ZER0poQ2N5VEMzOUNuWUxJZWxqYnlRVFNjQzJHeUhCalNNY21KMDJLSQ?oc=5" target="_blank">US security agency is using Anthropic's Mythos despite blacklist, Axios reports</a> <font color="#6f6f6f">Reuters</font>
 National Security
National SecurityReport: Cellular modules from Chinese companies in smart home devices are national security risk
A new report is warning that Chinese-produced cellular modules, tiny components that are inside smart home devices, present a significant national security risk for the United States. The Foundation for Defense of Democracies (FDD) report, first shared with The Hill, found that two Chinese firms, Quectel and Fibocom, control nearly half the global market for…
 National Security
National SecurityTrump’s Go-To Justification for Contentious Decisions: National Security
The administration has invoked national security in a variety of matters, including the White House ballroom and offshore wind farms, drawing rebukes from some judges.

Florida Opens Criminal Inquiry Into ChatGPT Tied to Fatal School Shooting - The New York Times
Did this story change how you see things?
Stories like this only matter when people see them. Help us get verified journalism in front of more eyes.
The Verity Ledger curates verified investigative journalism from trusted sources only.
See our sourcesMost Read This Week
Report: Merck’s blockbuster cancer drug topped $200,000 a year under Trump
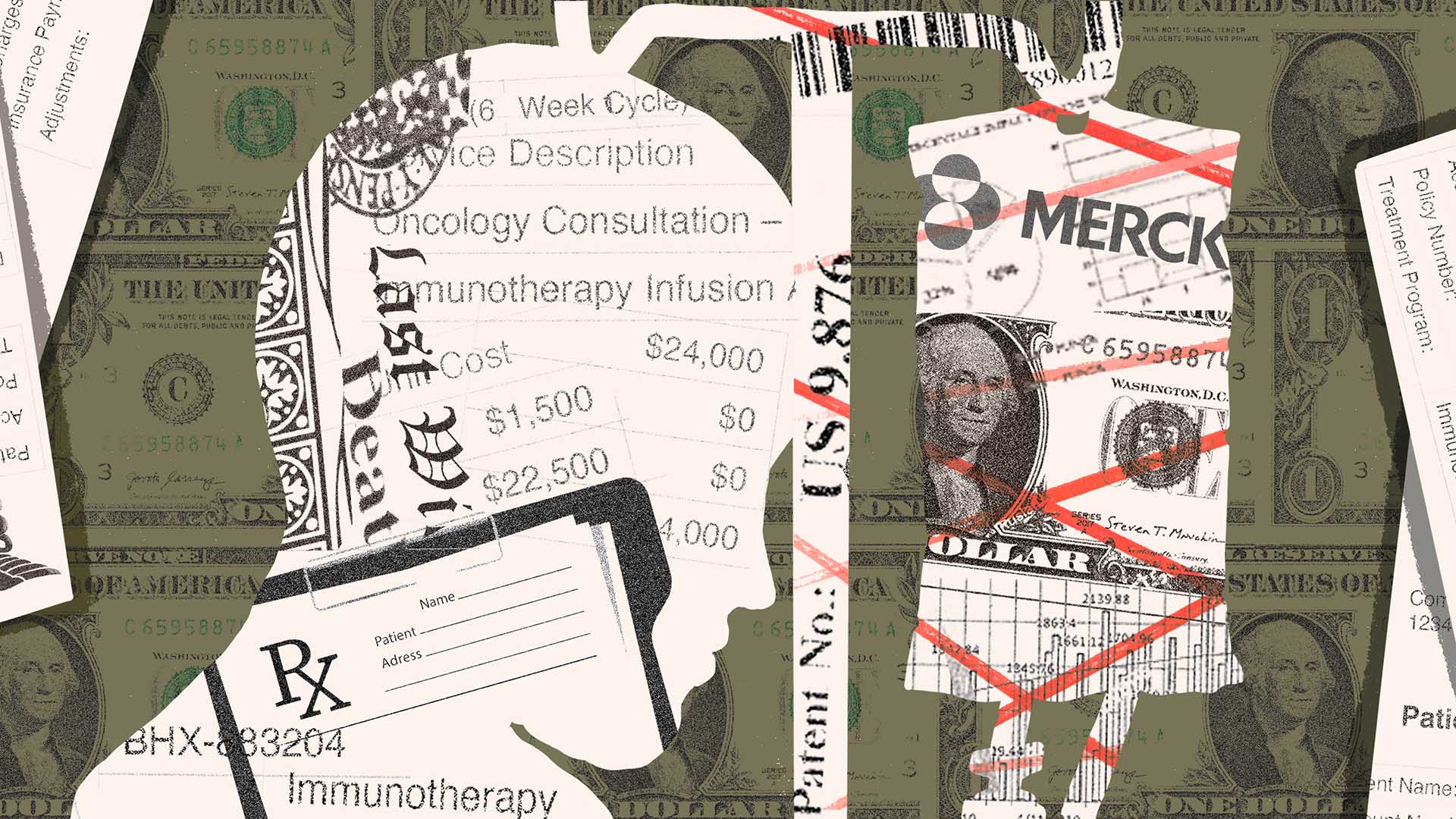
One in three Americans forced to make financial sacrifices for health coverage

Pope blasts ‘tyrants’ ravaging the Earth during his visit to Cameroon - AP News

Justice Jackson chides Supreme Court conservatives over 'oblivious' pro-Trump emergency orders - AP News

US Live Nation and Ticketmaster verdict triggers calls for Australian investigation into ticketing rules


